Regulated industries are deploying AI at a different pace. What exists for guidance was written before agentic AI became a reality in production. Most guidance assumes the organization has its own infrastructure, leaving architects who actually build on multi-tenant platforms to translate abstract policy into executable architecture on their own.
This article closes that gap. It presents Trust Boundary Control (TBC): a reference architecture for enforcing deterministic, auditable AI behavior directly within Salesforce using Salesforce Shield, Data 360 (formerly Data Cloud), and Flow as the enforcement layer, not as an afterthought.
Why Trust Control is Critical
The moment an enterprise automates decisions with AI, congratulations – you’ve just handed your risk and compliance team a brand new set of problems they didn’t ask for. Industries shift. Regulations don’t. Whether you are in Healthcare OEM, Finance, or Telecom OEM, one demand from your Design Authority Board (DAB) stays consistent: they don’t just want accurate AI decisions. They demand defensible ones. Accuracy gets applause. Defensibility keeps you out of a regulatory hearing.
If you are architecting Salesforce solutions in regulated industries, this isn’t theoretical – it’s your problem specifically. When loan approval algorithms flag a bias pattern, when an auditor demands proof that a medical device recommendation followed compliance protocol, or when GDPR requires you to show exactly how customer data crossed (or didn’t cross) regional boundaries, you need more than documentation. You need Trust Boundary Control (TBC).
TBC is the architectural framework that ensures data flow, AI inference, and process automation never violate core regulatory mandates. It shifts compliance from a paperwork exercise to an enforceable, automated design principle embedded directly into your Salesforce architecture – one that satisfies risk management requirements in NIST AI RMF and the documentation obligations under EU AI Act Article 9 by construction, not by retrospective audit.
This blueprint demonstrates how to use Salesforce Shield, Data 360 (formerly Data Cloud), and Flow to enforce TBC against the three threats that keep architects awake at night: Algorithmic bias, audit failure, and data localization violations.
Risk first means every control is traceable to a specific threat, not chosen by convention.
| Threat | What breaks | TBC Phase | NIST AI RMF |
|---|---|---|---|
| Algorithmic Bias | AI output systematically disadvantages a protected class | Phase I – Governance thresholds in CMDT | Govern, Map |
| Audit Failure | Regulator asks what your AI decided and why – you cannot show them | Phase II – Compliance shadow record + Audit chain | Manage, Measure |
| Sovereignty violation | Overnight identity resolution stitches profiles across jurisdiction silently | Phase III – Data spaces isolation + blocking rules | Map, Measure |
What AI at Scale Demands: Governance as Executable Architecture
The DAB (design authority board) meets. Documents are produced. Developers get a Confluence link and a deadline. This is not governance – this is governance theatre, and in regulated industries, it is genuinely expensive theatre when the audit arrives.
The fundamental problem is architecture, not culture. A policy document cannot intercept Apex callouts. A quarterly review cannot stop a flow from processing a high-risk decision at 2 AM on Sunday. Governance that lives outside the system cannot control the system.
In regulated environments, the consequences of that gap are not abstract:
- Healthcare OEM: PHI (Protected Health Information) crosses jurisdictional boundaries during overnight profile stitching – silently and without any audit trail.
- Finance: Insurance underwriting algorithms embed demographic risk proxies for months before monitoring surfaces it – by which point, the regulatory exposure has already compounded.
- Telecom OEM: AI-driven churn prevention models trained on CPNI (Customer Proprietary Network Information) data without consent verification, exposing carriers to FCC enforcement under 47 CFR part 64.
Traditional governance operates outside the system. Trust Boundary Control operates inside – as enforceable architecture, not aspirational policy.
Phase I: Governance as Design (Defining Trust Boundary)
The architectural process starts with the DAB defining rules as dynamic configurations, not static documents. This phase ensures governance becomes executable code that adapts without deployment cycles.
Making Governance Rules Executable
| Governance challenge | Architectural Mandate and Implementation |
|---|---|
| Algorithmic Bias | Mandate: TBC must prevent systematic unfairness bias in AI Output. Implementation: Use custom metadata types (CMDT) to store bias tolerance thresholds and XAI (Explainable AI) influence factors. This allows DAB to dynamically adjust governance rules without code deployment |
| Audit Failure | Mandate: TBC must guarantee verifiable, immutable records of every high-risk decision. Implementation: Design a Model Metadata Standard requiring AI Model version and Training Data Set ID to be linked and logged as immutable artifacts before deployment. |
| Human-in-the-loop (HITL) Enforcement | Mandate: High-risk decisions must always enforce HITL control. Implementation: Define a Reason Code Taxonomy deployed to CMDT. Every Flow processing high-risk AI decisions can only continue if the user provides an audit-ready Reason Code for overrides. |
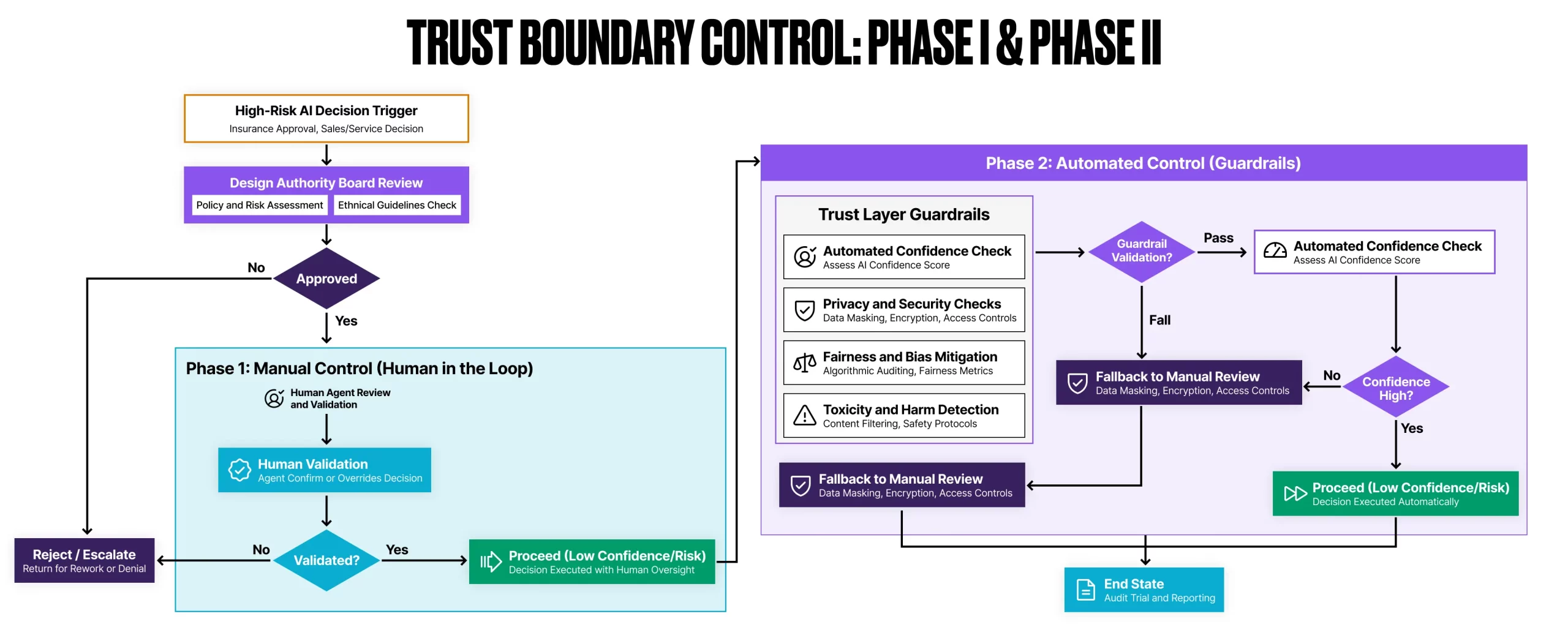
Phase II: Enforcement and the Compliance Shadow
This phase implements the HITL mechanism and creates an insulated, high-security audit ledger – what I call a compliance shadow record. Field Audit Trail is the retention layer that makes the Shadow Record non-repudiable. It is not enough to create the record – the platform must prevent its modification or deletion after the fact.
The Three-Layer Enforcement Strategy
- Enforcing HITL with Flow and Orchestrator: The architect designs the business process flow to stop at high-risk AI decision points. The Flow prompts users for a mandatory Reason Code if they override AI recommendations. This disagreement record becomes your most critical audit artifact: proof of active human judgment.
- The Compliance Shadow Record: Design a high-security custom object specifically as your audit ledger. Every critical decision point (AI score, XAI factors, HITL override reason) is logged here. This insulated, immutable record simplifies auditor reviews and creates a defensible compliance trail. EU AI Article 9 requires documentation that demonstrates risk management was applied.
- Off-Platform Audit chain: Configure your flow to only proceed after successfully calling an external API that writes Compliance Shadow Record data to an off-platform, immutable ledger (enterprise data lake or compliance vault). This guarantees a verifiable, third-party audit chain that survives org data retention policies.
Key Insight: The compliance shadow record operates independently of your primary business objects. Even if an opportunity or case record is edited, deleted, or corrupted, the audit trail remains intact. This separation is critical when auditors arrive 18 months after a decision was made.
Phase III: Data Security and Integrity
This phase establishes the physical and logical boundaries required to adhere to Data Localization mandates and prevent accidental data leakage across jurisdictions.
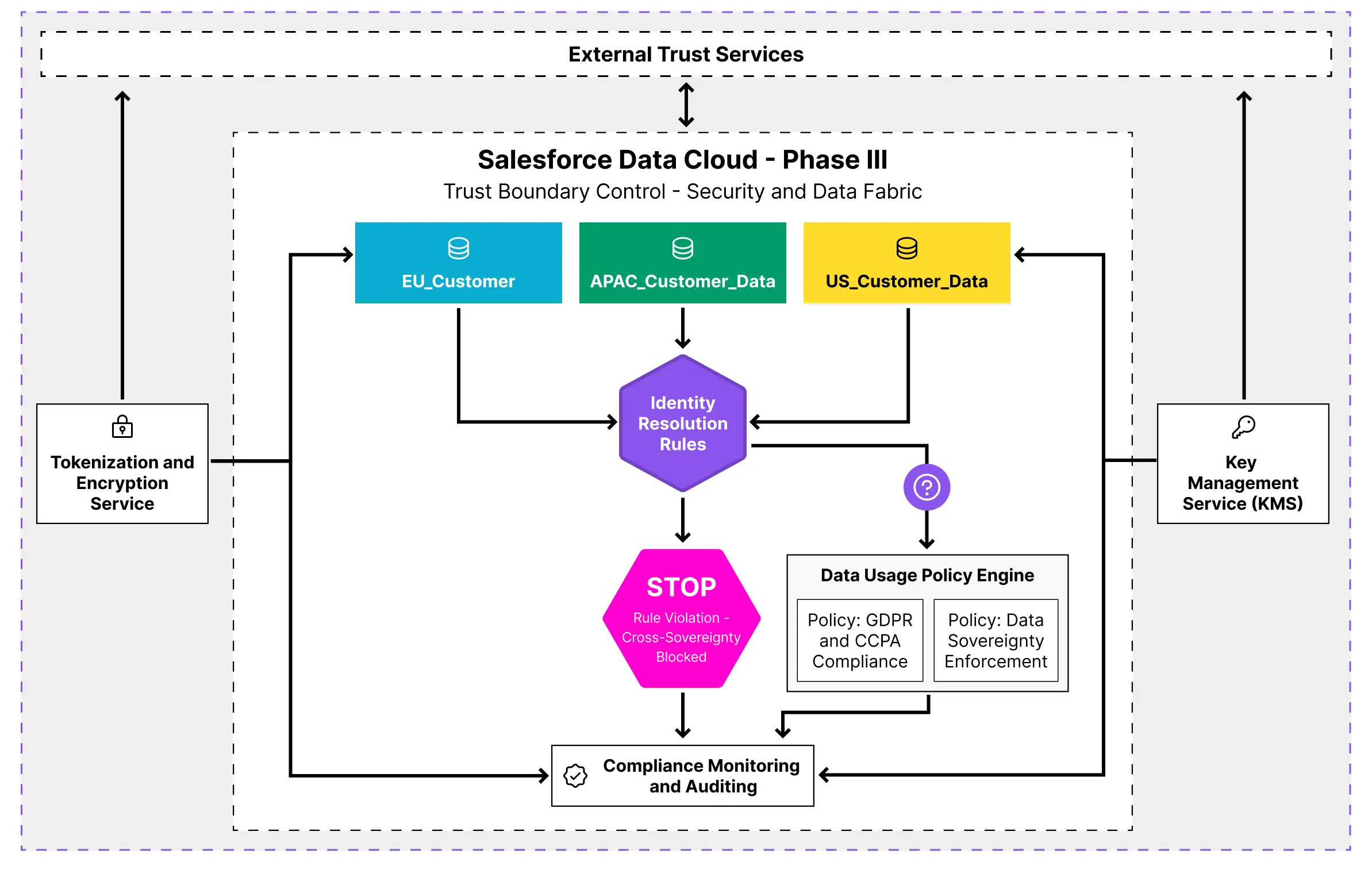
Data Space Architecture for Jurisdictional Isolation
| Security challenge | Architectural Mandate and Implementation |
|---|---|
| Geo-Segregation Fabric | Mandate: Adhere to Data Localization through logical partitioning. Implementation: Use Salesforce Data 360 to define Data Spaces that enforce data residency and access controls. This ensures PHI/PII remains isolated by jurisdiction. |
| Profile Aggregation Prevention | Mandate: Block profile stitching if it violates sovereignty mandates for every high-risk decision. Implementation: Configure Data 360 Identity Resolution rules to explicitly block stitching of localized, pseudonymized customer records when the resulting unified profile violates active data sovereignty requirements. |
| Trust Boundary Data Validation | Mandate: Ensure sensitive data is only processed by authorized users/code. Implementation: Apex must explicitly check data accessibility before processing sensitive fields. This is code-level Trust Boundary enforcement. |
Key Insight: This isn’t just about permissions. It’s about preventing data leakage by design. Before any field is sent to LLM, external API, or even logged for debugging, your code must explicitly validate access rights.
The Complete Trust Boundary Control Flow
This diagram shows TBC operating as a single cohesive system rather than three independent phases. Governance thresholds defined in CMDTs in Phase I feed directly into the HITL decision gates in Phase II. The flow cannot evaluate a risk threshold it hasn’t retrieved from configuration.
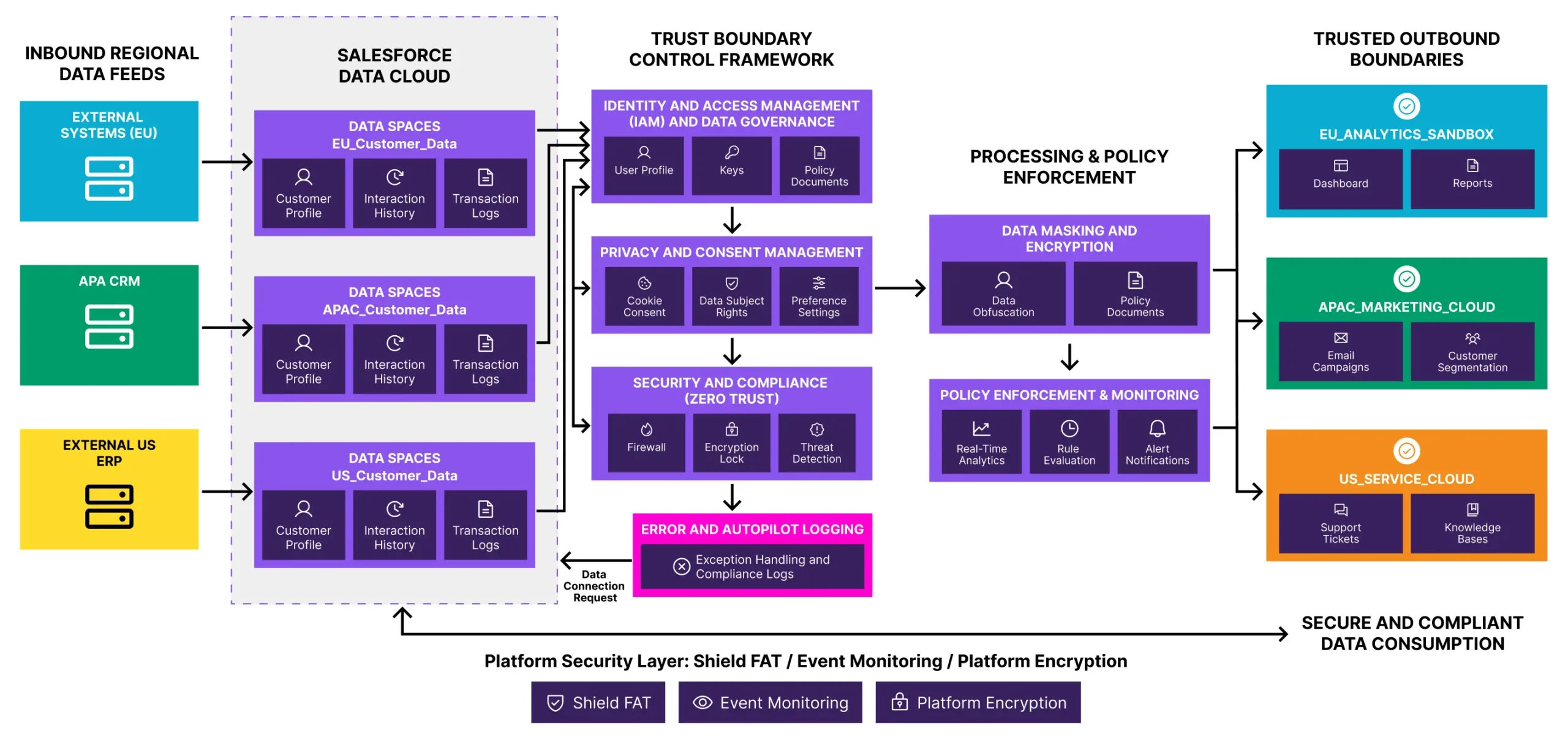
The Compliance Shadow Record in Phase II captures the outcome of every boundary decision before the process continues. Phase III’s data localization controls sit upstream of both – no AI inference runs against data that has not first passed jurisdictional validation. The dependency is intentional: each layer only operates on data and decisions that the previous layer has already cleared. Remove any one layer, and the audit trail has a gap. That gap is what regulators look for first.
Knowing where TBC architectures fail is as important as knowing how to build them. These three antipatterns represent the most common structural failures in regulated industry AI governance, and none of them are accidental.
Anti-Pattern 1: Adding Governance Later
- What happens: Teams build AI features first, then try to retrofit compliance. Result? The architecture fundamentally can’t support the audit requirements without complete rebuild.
- TBC Solution: Define governance rules in CMDTs before writing business logic. Your flows and apex should read from governance metadata from day one.
Anti-Pattern 2: One Compliance Shadow Record per Org
- What happens: Teams create a single compliance shadow object record with generic fields, trying to serve every decision type. It becomes unmanageable garbage.
- TBC Solution: Create decision type specific shadow objects (e.g Insurance_Approval_Audit__c, Medical_Device_Audit__c) with fields tailored to regulatory requirements for that domain.
Anti-Pattern 3: Data 360 Handling Sovereignty Assumption
- What happens: Architects assume Data 360’s data spaces automatically prevent sovereignty violations. They don’t configure Identity Resolution Rules, and profiles stitch across borders during overnight batch jobs.
- TBC Solution: Explicitly configure blocking rules in identity resolution. Test with cross-region data. Validate that the quarantine process triggers correctly. Don’t assume, verify.
Anti-Pattern 4: Shield as Sufficient
- What happens: Architects implement Platform Encryption and Field Audit Trail, present it to the DAB as compliant AI governance, and stop there. Shield secures data at rest and retains field history: it does not record what your AI system decided, against which risk threshold, or whether a human reviewed it before the process continued.
- TBC Solution: Configure FAT (field audit trail) retention policy explicitly against your regulatory obligation, enable Event Monitoring before you need it, and restrict decrypt permissions to roles with documented business justification. Then build TBC above all of it. Shield tells auditors your data was protected, TBC tells them your AI was governed. You need both statements to be true.
Measuring TBC Success: The Model Drift Remediation Cycle
The ultimate measure of your TBC architecture isn’t how many CMDTs you created – It’s your model drift remediation cycle time: how quickly can your DAB pull a non-compliant model, retrain it under correct governance rules, and redeploy it?
| Industry | Failure Mode | Target cycle time | Components Required |
|---|---|---|---|
| Healthcare OEM | PHI crosses jurisdictional boundaries during overnight profile stitching – silently, without audit. | < 72 hours | Cross-region data flow audit, Identity Resolution blocking rule validation, jurisdictional quarantine test, clinical change control sign-off. |
| Finance – Insurance | Underwriting algorithms embed demographic risk proxies for months before the end model surfaces it. | < 48 hours | Automated bias detection against protected class proxies, actuarial validation sign-off, and pre-approved retraining datasets. Blue/Green model deployment. |
| Telecom OEM | Churn prevention models trained on CPNI data without consent verification, exposing the carrier to FCC enforcement under 47 CFR part 64. | < 24 hours | CPNI consent verification audit, FCC 47 CFR part 64 compliance checklist, model rollback automation, A/B framework with consent-clean dataset. |
Stop Building Features, Start Building Boundaries
To every architect, consultant, or DAB reading this: The time to define your trust boundary control is now – before the next audit, before the next regulatory fine, before the AI decision that exposes your enterprise to material risk.
Here’s your 90-day roadmap:
Month 1 – Foundation
- Map high-risk AI decisions across your org.
- Define the governance threshold in the CMDTs.
- Design compliance shadow record structure.
- Audit current data flows for sovereignty violations.
Month 2 – Enforcement
- Implement HITL flows with reason code taxonomy.
- Deploy TBC validation utilities.
- Configure Data 360 data spaces.
- Test Identity Resolution blocking Rules.
Month 3 – Validation
- Run end-to-end compliance simulations.
- Measure Model Drift Remediation Cycle Time.
- Present DAB with audit-ready evidence packages.
- Document architectural decisions for future architects.
Final Thoughts
The DAB that commissioned your architecture shouldn’t have to explain your governance model when the auditor arrives.
If TBC is built correctly, the architecture explains itself – in logs, in configuration, in the compliance shadow record that tells the story of every decision in your AI system made, and every boundary respected.
That is what defensible architecture looks like.

